For English readers: You can find the English version under the Hungarian one.
Követve a dokumentációt, két pofonba lehet rögtön beleszaladni.
Az első: VPNUserAuthentication template could not find specified CSPs
Ha beállítjuk a fenti dokumentáció szerint a CA template-t és egy olyan gépen futtatjuk, ahol nincs TPM chip (például virtuális gép), akkor nem fog létrejönni a felhasználó tanúsítványa. A CertificateServicesClient-CertEnroll kliens sajnos alapból nem loggol semmit, úgyhogy még hibaüzenet sem lesz.
Az első teendő, hogy kapcsoljuk be a loggolást.
A registryben a HKLM\Software\Microsoft\Cryptography\Autoenrollment kulcs alatt hozzunk létre egy AEEventLogLevel DWORD bejegyzést, aminek 0 az értéke.
Ezután adjuk ki a gpupdate /force /target:user parancsot. (Nem szükséges újraindítás)
Az Event Viewer-ben nyissuk meg az Application Log-ot és megtaláljuk a következő hibaüzenetet:
Log Name: Application
Source: CertificateServicesClient-CertEnroll
Event ID: 55
Level: Warning
Certificate enrollment for DOMAIN\user for the VPNUserAuthentication template could not find specified CSPs on the local machine. Enrollment will not be performed.
Beszédes, nem?
(A CSP a Cryptographic Service Provider rövidítése)
Szerencsére van egy kis támpont, a dokumentációban, ez szerepel:
Microsoft Platform Crypto Provider lets you use the Trusted Platform Module (TPM) on client computers to secure the certificate.
…
On the Cryptography tab, complete the following steps:
In Provider Category, click Key Storage Provider.
Click Requests must use one of the following providers.
Select the Microsoft Platform Crypto Provider check box
Tehát csak akkor jön létre a cert, ha van TPM chip a gépben. A megoldás az, hogy megszerkesztjük a VPN User Authentication Template-t:
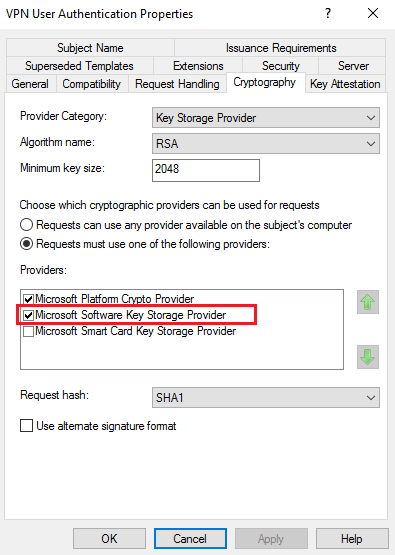
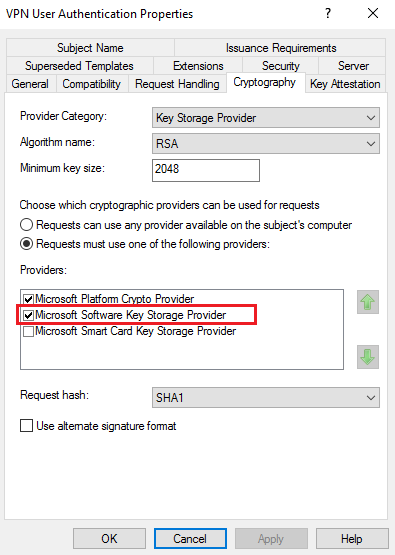
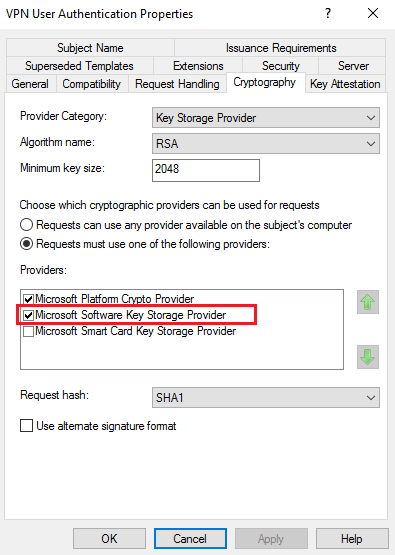
A certificate szerver kezelőjében jobb gomb a Certificate Templates mappán és Manage. Szerkeszük meg a VPN User Authentication template-t úgy, hogy a Cryptograpy alatt így nézzen ki:
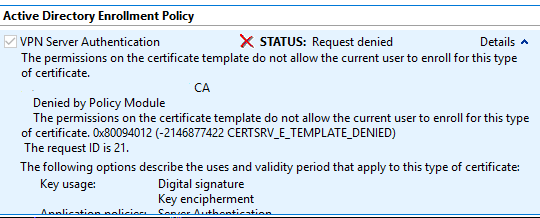
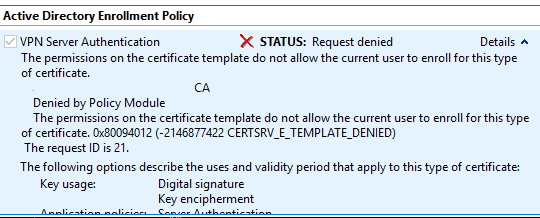
A másik probléma, hogy a VPN Szerver tanúsítványának kérésekor az alábbi hibaüzenetet kapjuk: CERTSRV_E_TEMPLATE_DENIED
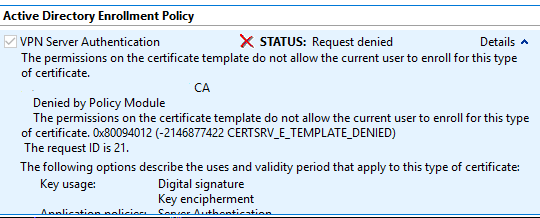
The permissions on the certificate template do not allow the current user to enroll for this type of certificate.
Denied by Policy Module
The permissions on the certificate template do not allow the current user to enroll for this type of certificate. 0x80094012 (-2146877422 CERTSRV_E_TEMPLATE_DENIED)
The request ID is 21.
Az ok: Azért fordul elő ez a hiba, mert tényleg nincs jogosultságunk. Ugyan hozzáadtuk a szervert a VPN Servers csoporthoz, de ahhoz, hogy a csoporttagságot felvegye a gép, újra kell indítani, ugyanis a windowsban a csoporttagságok bejelentkezéskor rendelődnek hozzá a tokenhez. Nincs ez máshogy a számítógép fióknál sem, azonban a gép csak induláskor jelentkezik be.
A megoldás: Újraindítjuk a VPN szervert és újrakéjük a certificatet.
________________________________________________________
English version
When you follow the Always On VPN documentation, you can run into the following issues.
ISSUE1: VPNUserAuthentication template could not find specified CSPs
If you set the User CA template according to the documentation and your computer doesn't have a TPM chip (running on VM for example), then the user certificate will not be created. Unfortunately, the CertificateServicesClient-CertEnroll doesn't log anything. First, set new registry key to turn on more detailed autoenrollment auditing: In HKCU\Software\Microsoft\Cryptography\Autoenrollment, create a new DWORD value named AEEventLogLevel and set its value to 0.
Open up Application Log in Event Viewer (eventvwr.exe).
Force Autoenrollment:
gpupdate /force
In the Application event log, refresh the log to see what happens during autoenrollment.
Log Name: Application
Source: CertificateServicesClient-CertEnroll
Event ID: 55
Level: Warning
Certificate enrollment for DOMAIN\user for the VPNUserAuthentication template could not find specified CSPs on the local machine. Enrollment will not be performed.
CSP means: Cryptographic Service Provider
Luckily in the documentation we can find the following:
Microsoft Platform Crypto Provider lets you use the Trusted Platform Module (TPM) on client computers to secure the certificate.
…
On the Cryptography tab, complete the following steps:
In Provider Category, click Key Storage Provider.
Click Requests must use one of the following providers.
Select the Microsoft Plaform Crypto Provider check box
So the certificate is only created if the computer has a TPM. The solution is to edit the VPN User Authentication Template.
On the CA, open Certification Authority.
In the navigation pane, right-click Certificate Templates, and click Manage, edit VPN User Authentication and select the Cryptography tab:
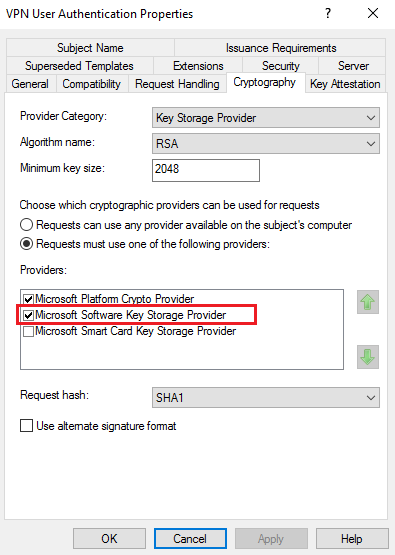
Add the Microsoft Software Key Storage Provider.
ISSUE2: CERTSRV_E_TEMPLATE_DENIED
The VPN Server certificate when you try to enroll, you get the following message:
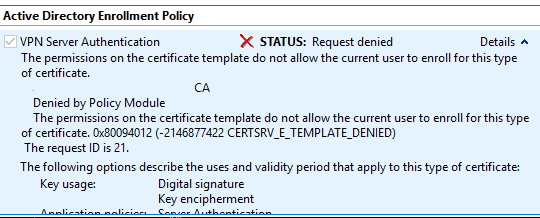
The permissions on the certificate template do not allow the current user to enroll for this type of certificate.
Denied by Policy Module
The permissions on the certificate template do not allow the current user to enroll for this type of certificate. 0x80094012 ( -2146877422 CERTSRV_E_TEMPLATE_DENIED )
The request ID is 21.
The solution: This is happens, because we added the computer to VPN Servers group – and set the permissions on the template to it -, but we didn't restarted the server. Restart the VPN server and try to Enroll again.